[fusion_builder_container hundred_percent=”yes” overflow=”visible”][fusion_builder_row][fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_title size=”1″]How to remove shortcut virus from USB – Dinihou – Houdini Worm.VBScript[/fusion_title]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”] [/fusion_imageframe]
[/fusion_imageframe]
[/fusion_builder_column][fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][xyz-ihs snippet=”720×90″]
[fusion_title size=”2″]What it is ? :[/fusion_title][ratings]
It’s a recent worm having already infected scores of computers all around the world. It is also called Houdini.
Depending on the antivirus used, it is detected as :
[fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- https://www.sosmalware.com/remove-wtdibpphwy-vbs-worm-vbs-dinihou-b/
- https://www.sosmalware.com/remove-elena-vbs-worm-vbs-dinihou-q/
- https://www.sosmalware.com/bibin-exe/
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
It is spread through USB peripherals such as pendrives, external drives, but also smartphones or digital cameras through their memory cards.
Once the media is connected, for users, the contents appear normal. Here’s a view showing 2 photos and a MP3 audio-file :
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”] [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”20″ style=”none”/]
But here is what the key really contains (which is “hidden” to users).
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”]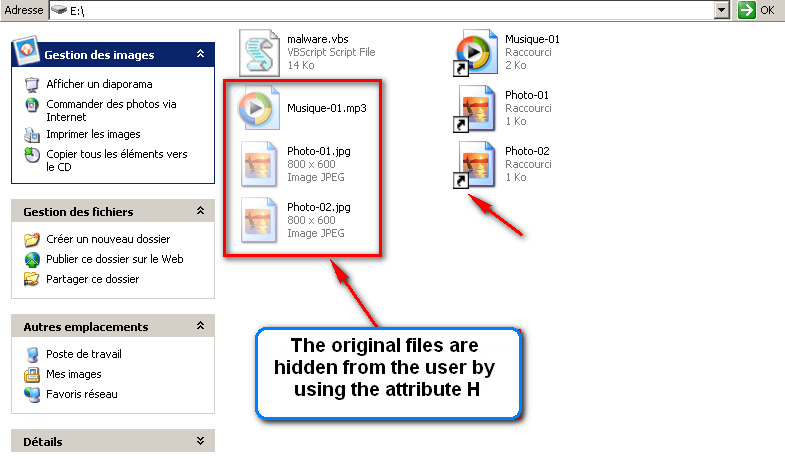 [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”20″ style=”none”/]
On the file on the right, we can notice a small arrow in the bottom left corner of the icon; it means this is a shortcut, and may be a sign of the infection
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”]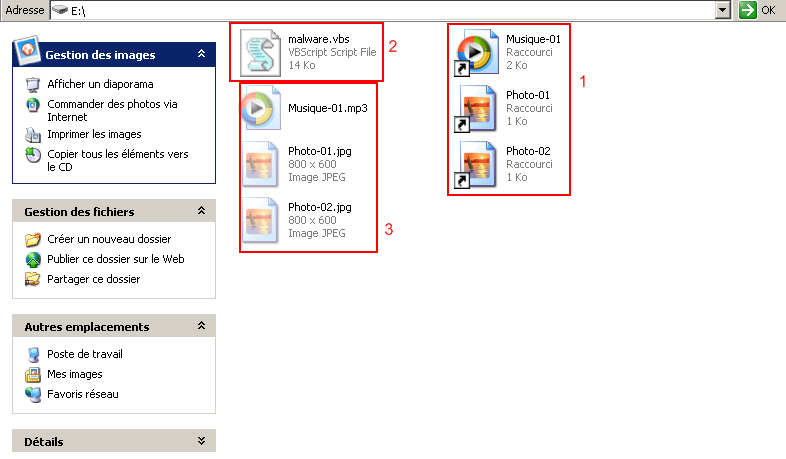 [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”20″ style=”none”/]
In 1, we can see the shortcuts (visible to users) and we may think they are real files; but in fact, these shortcuts, once clicked, will launch the infection (2) and then, open the original file (hidden to users).
You feel you have launched the file you wanted, and you won’t be aware the malware has been launched a few milli-seconds before.
YOU ARE CAUGHT!
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”]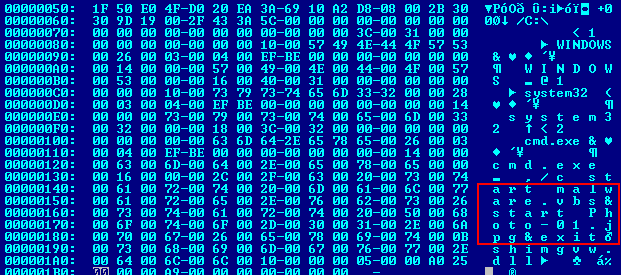 [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”40″ style=”shadow”/]
[fusion_title size=”2″]What it does ?[/fusion_title]
The file is a VBS (Microsoft Visual Basic script).
This type of script is commonly used by managers of operating systems and networks, to make small programs aiming at making repetitive tasks automatic.
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”]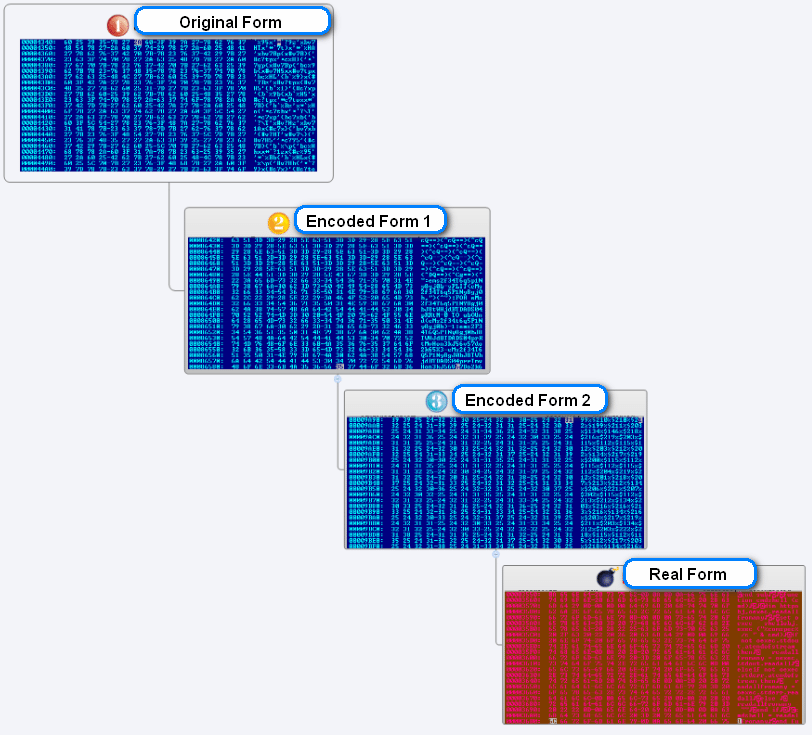 [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”20″ style=”none”/]
Without entering technique too much,let’s say the malware is complexly encoded to camouflage itself, and so avoid detection by anti-virus.
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”]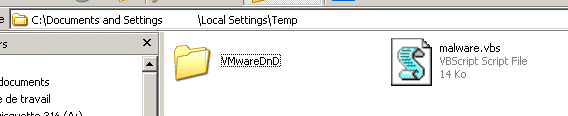 [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”]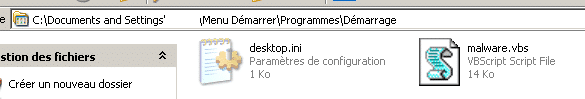 [/fusion_imageframe]
[/fusion_imageframe]
[fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- Once loaded into the memory (RAM) of the computer, the malware will make copies of its code in some precise folders of the system : temporary files and start.
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”]![]() [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”20″ style=”none”/]
[fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- It will make itself persistent, by creating 2 registry keys, in order to be launched when system re-starts
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”]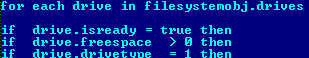 [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”20″ style=”none”/]
[fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- it, then, will search for all removable peripherals, and infect them, thus, making new vectors of propagation.
[/fusion_checklist]
[fusion_separator top=”40″ style=”shadow”/]
[fusion_title size=”2″]On the hacker’s side :[/fusion_title]
The malware connects to the C&C server, to transmit some information :
[fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- Serial numbers of drives
- Name of the computer and session
- Operationg system
- Name of the anti-virus (if any)
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”] [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”20″ style=”none”/]
The hacker, thus, will be able to take control of the “victim” computer to :
[fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- Steal data
- Update the malware (or delete it)
- Install other malwares
- He may also re-use the code, change it, enrich it
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
Here is a view of an ad for this type of malware :
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”] [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”20″ style=”none”/]
Here is a view of a managing console (what the hacker can see on his scren) :
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”] [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”]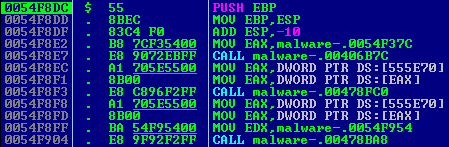 [/fusion_imageframe]
[/fusion_imageframe]
Even if the code is relatively simple, it is enough to corrupt the security of a whole organization, and retrieve personnal or confidential information from a great numberof people.
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”] [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”40″ style=”shadow”/]
[fusion_title size=”2″]What to do ?[/fusion_title]
[fusion_checklist icon=”fa-arrow-right” iconcolor=”#1e73be” circle=”no” circlecolor=”” size=”15px” class=”” id=””]
-
Not to be infected :
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
[fusion_builder_row_inner][fusion_builder_column_inner type=”1_2″ last=”no”]
See this article : https://www.usb-antivirus.com/2014/03/infections-spreading-usb-peripherals/
In particular the passage : “How to avoid this type of infection?”
We recommend you, either firms, or particulars, to adopt a full antivirus protection like Bitdefender Internet Security.
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center”] [/fusion_imageframe]
[/fusion_imageframe]
[/fusion_builder_column_inner]
[/fusion_builder_column][fusion_builder_column type=”1_2″ last=”yes”]
[fusion_title size=”3″]Bitdefender 2015 :[/fusion_title]
[fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- It offers protection against most viruses and other internet dangers
- Light, silent, and quick
- It protects your on-line shopping, and make your digital identification safe
- It informs you about your children’s activities, and provide filter tools if needed
- It integrates a firewall to protect your internet connexion
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
[fusion_button link=”https://www.bitdefender.com/Downloads/?cid=usb-fix-software” color=”custom” size=”large” type=”shake” shape=”square” target=”_blank” title=”Get Bitdefender” gradient_colors=”transparent|” gradient_hover_colors=”rgba(000,000,000,.05)|” accent_color=”#a0ce4e” accent_hover_color=”#96c346″ bevel_color=”” border_width=”2px” shadow=”no” icon=”fa-star” icon_position=”left” icon_divider=”yes” modal=”” animation_type=”0″ animation_direction=”up” animation_speed=”1″ alignment=”” class=”” id=””]Get Bitdefender[/fusion_button]
[/fusion_builder_column]
[fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_title size=”2″]If you are infected, UsbFix can deal with this type of infection.[/fusion_title]
[/fusion_builder_column][fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- Download UsbFix on your computer, and execute it.
- It will launch automatically, and a shortcut will be created on your desktop.
- Connect all your external data sources to your PC (Usb keys, external drives, etc…) Do not open them.
- Choose “Clean” option.
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=””] [/fusion_imageframe]
[/fusion_imageframe]
[/fusion_builder_column][fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- A pop-up will follow :
[/fusion_checklist]
Connect all your external data sources to your PC (Usb keys, external drives, etc…)
[/fusion_builder_column][fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- Once you’re ready, click “OK”.
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=””] [/fusion_imageframe]
[/fusion_imageframe]
[fusion_separator top=”20″ style=”none”/]
[/fusion_builder_column][fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- While cleaning, you will loose access to your desktop, but this is normal.
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=””]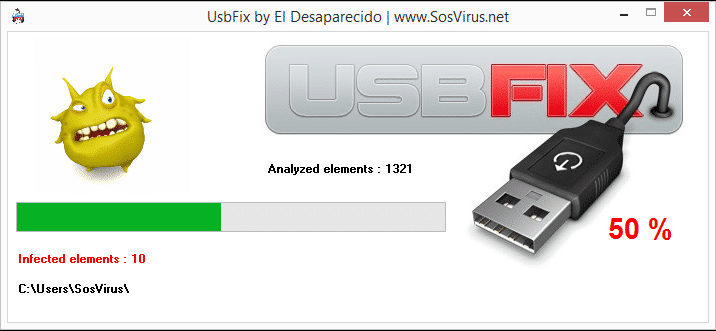 [/fusion_imageframe]
[/fusion_imageframe]
[/fusion_builder_column][fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- The numbers of analysed and infected éléments are displayed.
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=””] [/fusion_imageframe]
[/fusion_imageframe]
[/fusion_builder_column][fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- Once cleaning is over, you’ll be suggested to donate the author, El Desaparecido.
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=””]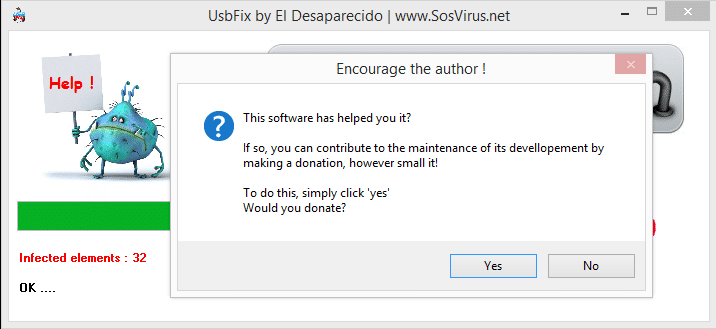 [/fusion_imageframe]
[/fusion_imageframe]
[/fusion_builder_column][fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- Donation is not compulsory, but is useful to go on developping the software, and meet the expense to maintain our website server.
- Once you’ve made a choice, a report will open.
[/fusion_checklist]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe style=”bottomshadow” lightbox=”yes” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=””] [/fusion_imageframe]
[/fusion_imageframe]
[/fusion_builder_column][fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_checklist icon=”star” iconcolor=”dark” circle=”no”]
- You can find a copy of this report on your desktop, and another at : C:\UsbFix\Log\UsbFix [Clean 1] Your PC.txt
- Copy/paste it on the board you’ve asked for help.
- If you are not taken care, we invite you to create a subject on the forum of disinfection SosVirus and to transmit the report for analysis.
[/fusion_checklist]
[/fusion_builder_column][fusion_builder_column type=”1_2″ last=”no” class=”” id=””]
[fusion_separator top=”20″ style=”none”/]
[fusion_imageframe lightbox=”no” style_type=”none” bordercolor=”#d1d1d1″ bordersize=”0px” stylecolor=”#ffffff” align=”center” link=”” linktarget=”_self” animation_type=”0″ animation_direction=”” animation_speed=”0.1″ class=”” id=””] [/fusion_imageframe][/fusion_builder_column][fusion_builder_column type=”1_2″ last=”yes” class=”” id=””][fusion_text]
[/fusion_imageframe][/fusion_builder_column][fusion_builder_column type=”1_2″ last=”yes” class=”” id=””][fusion_text]
Free Support
[/fusion_text]
[fusion_button link=”https://www.sos-virus.net/” color=”custom” size=”large” type=”shake” shape=”square” target=”_blank” title=”Free support” gradient_colors=”transparent|” gradient_hover_colors=”rgba(000,000,000,.05)|” accent_color=”#a0ce4e” accent_hover_color=”#96c346″ bevel_color=”” border_width=”2px” shadow=”no” icon=”fa-star” icon_position=”left” icon_divider=”yes” modal=”” animation_type=”0″ animation_direction=”up” animation_speed=”1″ alignment=”” class=”” id=””]Forum SosVirus[/fusion_button]
[fusion_separator top=”20″ style=”none”/]
[fusion_button link=”https://www.usb-antivirus.com/tutorial/” color=”custom” size=”large” type=”shake” shape=”square” target=”_blank” title=”Tutorial” gradient_colors=”transparent|” gradient_hover_colors=”rgba(000,000,000,.05)|” accent_color=”#a0ce4e” accent_hover_color=”#96c346″ bevel_color=”” border_width=”2px” shadow=”no” icon=”fa-star” icon_position=”left” icon_divider=”yes” modal=”” animation_type=”0″ animation_direction=”up” animation_speed=”1″ alignment=”” class=”” id=””]All Tutorial[/fusion_button]
[/fusion_builder_column][fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_separator style_type=”shadow” top_margin=”40″ bottom_margin=”40″ sep_color=”” icon=”” width=”” class=”” id=””/][/fusion_builder_column][fusion_builder_column type=”1_2″ last=”no” class=”” id=””][fusion_text]
[/fusion_text][/fusion_builder_column][fusion_builder_column type=”1_2″ last=”yes” class=”” id=””][fusion_title size=”3″ content_align=”left” style_type=”” sep_color=”” class=”” id=””]Rate this post :[/fusion_title][fusion_separator style_type=”none” top_margin=”20″ bottom_margin=”” sep_color=”” icon=”” width=”” class=”” id=””/]
[fusion_text][ratings][/fusion_text][/fusion_builder_column]
[fusion_builder_column type=”1_1″ background_position=”left top” background_color=”” border_size=”” border_color=”” border_style=”solid” spacing=”yes” background_image=”” background_repeat=”no-repeat” padding=”” margin_top=”0px” margin_bottom=”0px” class=”” id=”” animation_type=”” animation_speed=”0.3″ animation_direction=”left” hide_on_mobile=”no” center_content=”no” min_height=”none”][fusion_separator top=”40″ style=”none”/][/fusion_builder_column][/fusion_builder_row][/fusion_builder_container]



i got an error, 44205,,, what is this?
but it worked anyway! THANX a zillion! :-)
Sorry I am somewhere I can’t donate from…
hello!! so i tried it on my computer. and i checked my usb and those little shortcut arrows disappeared. does that mean my computer and usb is now safe to use (safe for other usbs and for other computers)? if so thanks so much!!! can’t donate right now but i’ll definitely share it!!
sorry i’m pretty much a noob and desperate since i’m almost at the end of my thesis. i think i saw a fellow university student here who experienced the same problem. can’t remember which computer shop i got it from though.
checking if letting to comment
thanks even though I had to format my system some time ago because I could not get rid of it by any means then. wish I had this software then
I will try it thnxs
TE AMOOOO!!!!!!
THANK YOU SO MUCH!!!!!
thanks
THANK YOU GUYS! YOU’RE SUCH A BIG HELP! MORE POWER TO ALL OF YOU!!
Thanks, it worked. You guys just saved my day!
Voy a probarlo!!. Muy buena la explicación.
thanks guys….i am fully relieved!!!
Woow. This software is a life saver my autorun problem is now solved. :))
Thanx, USBFix remove the virus succefully after a lot of tries with other tools .. thanx again ..
this totally works, thankyou! i tried so hard to remove the shortcut virus from USB/ flash drive and nothing worked, but USBFIX did the work in less than 5 minutes thankyou!
thank you very much. realy it works….
1st thank u very much for your hard work
2nd there is no other solution on the web dose any thing for this shortcut virus
i searched for 5 days and crabs keep coming up rather from youtube or another shit site
but you are a pro , this usbfix worked perfectly and remove the virus from my labtop and my flash-driver
thank you again
thanku….vry much yo guyz save my laptop thankuuuuuuu thankuuuu am vry fan of urs usb fix
its..just not only work its totally fucked tha..basterd shortcut virus am vry haappy to downlod this thank
It’s hard to find your blog in google. I
found it on 22 spot, you should build quality backlinks , it will help you to rank to google top 10.
I know how to help you, just type in google – k2 seo
tips
Thanks a lot for saving me from my frustration. I have tried antiviruses and malwares but non fixed this problem. Thanks t USBFix I was able to fix the shortcuts. God bless you.
perfect explanation, i will try to fix it, it also infect my symbian nokia e7 with word wia bluetooth…
This was probably the most informative and easy to understand article I have read in a long time! I actually understood it and learned from it.
Thank you so much!
thank u it really worked. i have shared it on my facebook wall. may others benifit from it.btw i noticed a small thing. if any virus file is being accesed by your app then avira antivirus will pop up and ur process is paused even though i deactivated avira realtime protection
oh…it really works welll…thanks for the developer
It really worked !!!!!! Thank you very much….I recommend it for all who are facing problems from vbs virus…
Thank you very much, it really worked, this worm was just annoying, good job guys
wow thanks guys this really works , this virus really had its effect on me but your meathod solved the problem with out deleting my files thanks
For months, I was worrying whether I will be able to view my data and photos.Wow! USBFix is certainly doing a wonderful job by removing the shortcut virus. However, it is not permanently solving the problem. Everytime I attach my mobile hard disk, I find the shortcuts appearing again and I have to use USBFix. Also, there is no information on what is ‘vaccination’. Could anyone guide me on how to fix the shortcuts permanently. Thanks in advance.
Hi,
So, connect this disk on your computer and Run UsbFix with Clean option : )
For “vaccination”, in french sorry .. , La vaccination à l’heure actuelle n’est plus vraiment utile car Microsoft depuis Windows Vista, a désactivé la lecture automatique des médias amovibles.
Il est vrai que je communique peut sur ce point. Tout simplement parce que je travail sur une nouvelle méthode de vaccination qui se transformera certainement par un module de protection en temps réel.
Best Regards.
Sir, what I am asking is whether there is any solution for permanently solving the problem without running USBFix again and again, because, eventhough I clean with USBFix, everytime I remove the mobile hard disk and attach it again to the computer, the shortcuts are reappearing.
Best regards.